The Mosaic Platform by Transmit Security enables advanced Business-to-Business (B2B) Customer Identity and Access Management (CIAM) experiences, which is now known in the industry as B2B CIAM. While Business-to-Consumer (B2C) access has been around for a long time, CIAM has generally focused on B2C rather than on B2B use cases. However, B2B scenarios introduce more complexity and demand greater customization from the CIAM platform vendor. The following list demonstrates some of the differences between B2C and B2B capabilities in CIAM:
- In B2C, user accounts are represented as a single (albeit very large) flat list of user accounts, while B2B introduces the concept of an organization, and its members.
- In B2C, although there may be millions of user accounts, the concept of user roles and role-based access control (RBAC) is less relevant. In B2B, end users have usually different roles and permissions in the context of an application, while in most B2C scenarios all end users have the same set of privileges in an application.
- In B2C, there is no need for delegated administration, because in most cases, end users simply sign up in a self-service manner. However, in B2B, there is usually a concept of an organization administrator, and there is much more of a need for organization administrators to onboard/offboard their own staff to specific applications, assign application roles, etc.
- Specifically, in Transmit, there is also a concept of an organizational hierarchy, whereby an organization can actually onboard another organization to access an application (where the child organization is known as a managed organization).
- Because there is a native concept of an organization, it is possible to customize Single Sign-On (SSO) experiences on a per-application per-organization basis (e.g. for example, to federate with the organization’s SAML Identity Provider).
One of the core concepts in Transmit Security is the ability to onboard/assign an organization to an application or to multiple applications. The following diagram illustrates this concept:
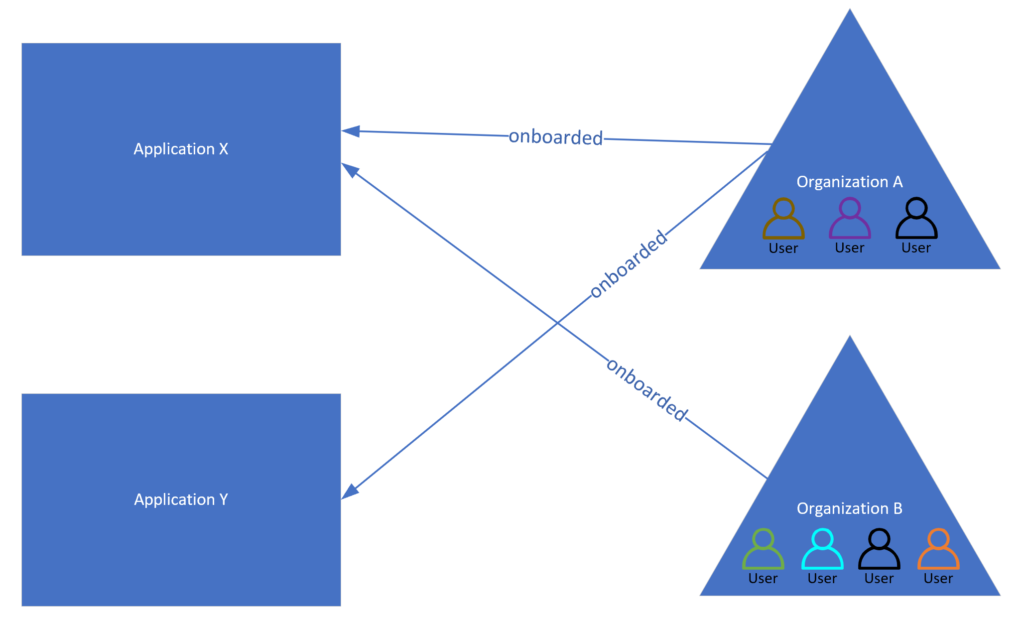
Each organization contains members (e.g., user accounts), and so any given member can have access to one or more applications. For example, in the diagram above, Organization A has been onboarded (i.e. assigned) to Application X and Application Y, which means a member of that organization can receive access to Application X, Application Y, or both. In contrast, Organization B has only been onboarded to Application X, which implies that members of this organization can only access Application X. The diagram also demonstrates that there is a user that is multi-org (shown with a black outline), meaning that the user is a member of both Organization A and Organization B. Therefore, if this specific multi-org user attempts to authenticate to an application, Transmit will ask the user to choose the organization on behalf of which the user is authenticating so that there is no ambiguity.
In general, the ability to manage members in an organization can be achieved in several ways, and is similar to the way this is achieved using other CIAM products on the market (such as Auth0 by Okta):
- Admin Portal
- This is the primary Admin Portal and is designed exclusively for access by CIAM administrators only
- Does not support the concept of delegated administration
- Organization and Member APIs
- Applications can develop their own UI/UX and invoke Mosaic APIs to onboard/offboard members to organization(s) via their own application(s)
- Supports the concept of delegated administration
- Self-Service Portal (also known as the Organization Admin Portal)
- Transmit offers a dedicated self-service portal that allows organization admins to manage their own members
- Supports the concept of delegated administration
As described above, Transmit supports the concept of a multi-org member, which means that a person with an identifier such as an email address can exist in multiple organizations. Therefore, during the login flow, Transmit will use the identifier of the user, potentially in combination with the organization information, to determine the organization that the user is authenticating on behalf of.
When developing your application, it’s important to keep in mind whether the application is B2C-only, B2B-only, or an application that supports both B2C and B2B scenarios.
Finally, it is important to point out that user accounts and organizations belong to a Transmit tenant/directory. Inside a tenant, there is a user profile repository that exists with all the user accounts in the tenant. When members are invited to organizations (for example via an email address), a user profile is also created for the user account if it doesn’t already exist, and it contains tenant-level data such as the user’s email address and user identifier (user_id). Importantly, these are the same regardless of which organization(s) the user is a member of. Therefore, when a member is invited to an organization, a corresponding user profile is also created for the user if doesn’t already exist, and that user profile contains tenant-level yet organization-agnostic data for the user.
To conclude, the Mosaic Platform of Transmit Security has a lot of advanced functionality, especially for B2B CIAM use cases. Since an organization is a core concept of the platform, it can support B2B sign-up and sign-in flows, in addition to more traditional B2C flows. Each organization has a name, domains, and an organization identifier (organization_id) that uniquely identifies it, along with members that can be invited and removed as described above.
Transmit Security enables advanced customization, especially for more complex B2B CIAM scenarios. There are a lot of other capabilities that are available which were not discussed in this article, but if you have a use case for B2B CIAM and need more advanced functionality, especially around delegated administration, you can take a look at Transmit’s Mosaic Platform and its capabilities.